| ID |
Date |
Author |
Author Email |
Category |
Subject |
Status |
Last Revision |
|
13
|
Thu Apr 28 15:45:58 2005 |
Alex H | alexsynergie-infcom | Theme/Skin | Bubble for pleasure by L'ange noir | Stable | Mon Aug 1 09:35:26 2005 by Alex H |
The original theme is from Francois Cukier but I have change a some color
and font.
Francois Cukier said : "Uncompress "Bubble.zip" in your Elog default
folder if you want to replace the original elog theme. Otherwise, if you
decompress it in another folder, you will need to modify your elogd.cfg
file as described at this adress: http://midas.psi.ch/elog/config.html"
Do it at the same ;o)
I want to thanks Francois Cukier and Stephan Ritt for their works, so
THANKS a lot !
I wait your comments :o).
-UPDATE------------------------------------------------------------------------
2005/08/1 : Alexander Sheremet correct CSS bug thanks to it, archive re-uploaded |
| Attachment 1: bubble2-1.gif
|
|
| Attachment 2: bubble2-2.gif
|
|
| Attachment 3: Bubble.zip
|
|
14
|
Fri Jul 8 17:34:02 2005 |
Emiliano Gabrielli | AlberT@SuperAlberT.it | Script | JavaScript list auto-refresh | Stable | Tue Jul 12 12:36:16 2005 by Emiliano Gabrielli |
Here is a simple piece of JS code to accomplish a smart page reload.
We don't reload if in some kind of editing mode.
You can put the code everywhere you like in the elog html page, my suggestion is to put it in Bottom Text (or Top Text):
;auto-refresh
Bottom text = [I]<script language="JavaScript">if (null==window.location.href.match('/[0-9]+$|.*(cmd|select)=.*') ) { window.setTimeout("location.reload();", 2*60*1000); now=new Date(); document.write('<br/>Last reload at '+now.getFullYear()+'/'+(now.getMonth()+1)+'/'+now.getDate()+', '+( ((h=now.getHours())<10) ? '0'+h :h)+':'+( ((m=now.getMinutes())<10) ? '0'+m :m)+':'+( ((s=now.getSeconds())<10) ? '0'+s :s)) }</script>[/I]
the timer is a product of # of minutes, #of seconds and milliseconds... 2 minutes in the above example 
| Revision Tue Jul 12 12:36:16 2005 wrote: |
modified regular expression in order to not activate the auto-refresh in the signle entry view
|
|
|
15
|
Thu Jul 28 18:42:48 2005 |
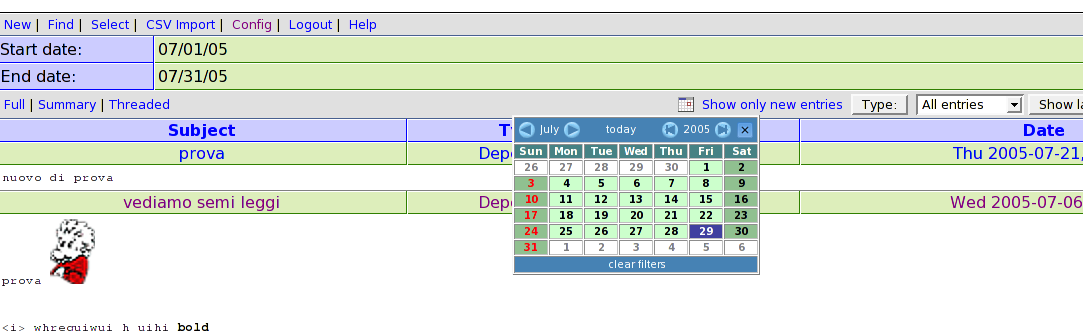
Emiliano Gabrielli | AlberT@SuperAlberT.it | Other | [New Feature]: JS calendar filter | Beta | Thu Aug 4 11:20:36 2005 by Emiliano Gabrielli |
NOTE:
it seems that for some strange reason it slows down elog very much when and only when elog is stunneled over ssl!
The attached tarball contains a full featured JavaScript allowing everyone to use a JS calendar (no popup windows, just JS and CSS!) to perform date-based filtering actions. An uncompressed version and the tarball for the last cvs rvision of this script is available at www.SuperAlberT.it
You can browse the ChangeLog here.
A simple way to use it is to uncompress the wall package into the elog data dir, under the "scripts" subdir.
the you can add the following code to your elog.cfg:
Filter Menu text = scripts/calendar_filter/calendar_filter.html
note that this configuration parameter is available in elog starting from
Revision 1.732 2005/07/29
and automagically have the new calendar_filter icon showed 
 |
| Attachment 2: elog_calendar_filter-1.0.1.tar.gz
|
|
16
|
Wed Sep 7 16:52:30 2005 |
Peter Eriksson | peter@ifm.liu.se | Other | Solaris 10 SMF/Greenline management manifest for ELog | Stable | |
Please find enclosed as an attachment a Solaris 10 SMF/Greenline manifest that can be used to manage ELog.
(If you don't know what it is - it replaces init.d/cron/inittab and more stuff) |
| Attachment 1: elog.xml
|
<?xml version="1.0"?>
<!DOCTYPE service_bundle SYSTEM "/usr/share/lib/xml/dtd/service_bundle.dtd.1">
<!--
Copyright (c) 2005-06-17 Peter Eriksson (peter@ifm.liu.se)
This manifest can be used to manage an elog daemon using the
Solaris SMF subsystem.
Import this manifest using:
svccfg -v import elog.xml
Then activate the daemon with:
svcadm enable site/elog
-->
<service_bundle type='manifest' name='IFM:elog'>
<service
name='site/elog'
type='service'
version='1'>
<single_instance />
<!-- Need / & /usr filesystems mounted, /var mounted read/write -->
<dependency
name='fs-local'
type='service'
grouping='require_all'
restart_on='none'>
<service_fmri value='svc:/system/filesystem/local' />
</dependency>
<dependency
name='network-service'
grouping='require_all'
restart_on='none'
type='service'>
<service_fmri value='svc:/network/service' />
</dependency>
<dependency
name='name-services'
grouping='require_all'
restart_on='refresh'
type='service'>
<service_fmri value='svc:/milestone/name-services' />
</dependency>
<exec_method
type='method'
name='start'
exec='/ifm/sbin/elogd -D -c /ifm/etc/elogd.cfg'
timeout_seconds='60'>
</exec_method>
<exec_method
type='method'
name='stop'
exec=':kill'
timeout_seconds='30'>
</exec_method>
<instance name='default' enabled='false' />
<stability value='Evolving' />
<template>
<common_name>
<loctext xml:lang='C'>
Electronic Logbook server
</loctext>
</common_name>
<documentation>
<manpage title='elogd' section='1' manpath='/usr/local/man' />
</documentation>
</template>
</service>
</service_bundle>
|
|
17
|
Mon Oct 10 18:47:09 2005 |
Exaos Lee | Exaos.Lee@gmail.com | Script | How to run elogd on Gentoo Linux | Stable | Tue Oct 11 08:06:55 2005 by Stefan Ritt |
| I have created some scripts for running elogd on Gentoo Linux. Please untar the attachment and read the file "elogd_gentoo_readme". Any comment is welcomed. |
| Attachment 1: elogd_gentoo.tar.gz
|
|
18
|
Mon Sep 25 11:24:05 2006 |
Yoshio Imai | | Documentation | securing of elog with stunnel v4 under Linux | Beta | |
| The following instructions should work in securing the elog using stunnel version 4 under Linux. The specific paths may have to be adapted to your distribution. A sample configuration file is attached. |
| Attachment 1: elog-stunnel4.howto
|
1. Prepare a certificate
------------------------
either: request a certificate for your elog URL from your web administrator
- the private key must not be password-protected
- the 'common name' must be the URL of your elog server
or: create a self-signed certificate yourself with the OpenSSL package
- as root user, create a self-signed certificate with the command
root@localhost:# openssl req -new -x509 -config /etc/ssl/openssl.cnf -keyout stunnel.pem -out stunnel.pem -days 365 -nodes
- this creates a self-signed certificate (-x509) whith one year validity (-days 365)
and no password protection for the private key (-nodes)
- private key and certificate are written to the same file, "stunnel.pem"
Answer all questions, making sure that the 'common name' is the URL under which users
are to reach your elog server.
For more information on how to create and/or manage SSL certificates, see e.g.
http://www.ibiblio.org/pub/Linux/docs/HOWTO/SSL-Certificates-HOWTO
Notice: Unless your web administrator can procure a certificate signed by an established
CA, your elog users will be asked if they want to accept your (unverifiable) certificate
when connecting to your elog server. This is no problem at all but can lead to
questions if your users are unsure about this.
2. Adapt the certificate file to stunnel4 conventions
-----------------------------------------------------
The certificate filename must be the MD5 checksum:
- Retrieve the MD5 checksum of your certificate with
root@localhost:# openssl x509 -hash -noout -in stunnel.pem
abcdefgh
- Rename the certificate file accordingly
root@localhost:# mv stunnel.pem abcdefgh.0
- Move the certificate file to the standard location, e.g. /etc/ssl/certs
- change the permissions of the file to -rw-------
- make sure there is a blank line between
-----END RSA PRIVATE KEY----- and -----BEGIN CERTIFICATE-----
and a blank line after
-----END CERTIFICATE-----
in your certificate file.
3. Configure stunnel4
---------------------
Install the stunnel4 package (if not already done).
Modify the configuration file (e.g. /etc/stunnel/stunnel.conf, depending on your
distribution):
- general options:
cert = /etc/ssl/certs/abcdefgh.0 ; put the name of your certificate file here
debug = 4 ; otherwise ALL connection attempts will be logged to your syslog
pid = /var/run/stunnel4/stunnel.pid ; check where the other services write their pid-files, depends
; somewhat on the distribution
- comment out all lines containing chroot options
- comment out all CA lines
- comment out all service sections except the HTTPS section, which should look as follows
[https]
accept = 443 ; i.e. stunnel listens on port 443, the standard https port
connect = 8080 ; and forwards all connections to port 8080 (use the port under which
; your elogd is running here!)
TIMEOUTclose = 0 ; for buggy MS Internet Explorers, see the stunnel4 manpage
Some Linux distributions require that in the file /etc/defaults/stunnel4 the option ENABLED be set
to ENABLED=1. If not, the stunnel will not be started at system bootup.
4. Start the stunnel4 server
----------------------------
root@localhost# stunnel4 /etc/stunnel/stunnel.conf
Your elog should now be accessible via
https://your.elog.server
|
| Attachment 2: stunnel.conf
|
cert = /etc/ssl/certs/abcdefgh.0
pid = /var/run/stunnel4/stunnel.pid
; Some performance tunings
socket = l:TCP_NODELAY=1
socket = r:TCP_NODELAY=1
; Some debugging stuff useful for troubleshooting
debug = 4
; Service-level configuration
[https]
accept = 443
connect = 8080
TIMEOUTclose = 0
|
|
19
|
Sat Oct 21 02:23:17 2006 |
Leo Souza | leo@leo.com | Documentation | teste abc | Stable | 1.0 |
| alksjdkajklasjdas |
|
20
|
Wed Jan 10 23:08:27 2007 |
Exaos Lee | Exaos.Lee@gmail.com | Script | Script for running ELOGD on Ubuntu Linux | Stable | |
I prepared one init script for ELOGD running on Ubuntu Linux.
Please see the attachment. |
| Attachment 1: elogd_ubuntu.tgz
|
|
21
|
Tue Feb 20 18:20:40 2007 |
Val Schmidt | vschmidt@ldeo.columbia.edu | Documentation | Secure elog with SSL under Apache2 on Ubuntu | Stable | |
The steps for configuration under Apache2 are a bit different. Below I've included a quick list of instructions for Ubuntu. One nice thing about this method, is that only https requests to https://your.url/elog are redirected (not all https connections to your url) so you can have other services running under ssl:
My Setup:
Ubuntu 6.10 (Edgy):
Linux tide1 2.6.17-11-generic #2 SMP Thu Feb 1 19:52:28 UTC 2007 i686 GNU/Linux
Packages:ii apache2 2.0.55-4ubuntu4 next generation, scalable, extendable web se
ii apache2-common 2.0.55-4ubuntu4 next generation, scalable, extendable web se
ii apache2-mpm-worker 2.0.55-4ubuntu4 high speed threaded model for Apache2
ii apache2-utils 2.0.55-4ubuntu4 utility programs for webservers
ii elog 2.6.1+r1642-1 Logbook system to manage notes through a Web ---
To setup ssl in apache2 for elog I started here:
This min-howto was kindly provided in a forum. I reproduced it here without permission.
A Mini-Howto for apache2:
apt-get install apache2
apache2-ssl-certificate
(and answer the questions)
Now, enable ssl:
a2enmod ssl
configure ssl:
cp /etc/apache2/sites-available/default /etc/apache2/sites-available/ssl
ln -s /etc/apache2/sites-available/ssl /etc/apache2/sites-enabled/ssl
"/etc/apache2/sites-enabled/ssl" should look like this:
NameVirtualHost *:443
<VirtualHost *:443>
(... configure the directories too...)
and "/etc/apache2/sites-enabled/default" should look like this:
NameVirtualHost *:80
<VirtualHost *:80>
(... configure the directories too...)
In /etc/apache2/ports.conf, add Listen 443
In the middle of /etc/apache2/sites-available/ssl file, insert this two lines:
SSLEngine On
SSLCertificateFile /etc/apache2/ssl/apache.pem
Hope it helps :)
This method, without configuraiton of any of the <Directory> directives in /etc/apache2/sites-available/ssl, makes everything in /var/www https accessible. This may not be desirable. Configure the directives as you see fit.
To get SSL forwarding going for elog, in /etc/apache2/sites-available/ssl, I added the following:
ServerName tide1.unh.edu
ProxyRequests Off
ProxyPreserveHost On
<Location /elog/>
Order allow,deny
allow from all
ProxyPass http://tide1.unh.edu:8080/
ProxyPassReverse http://tide1.unh.edu:8080/
SSLRequireSSL
</Location>
Once this is in place one must restart apache with
sudo /etc/init.d/apache2 force-reload
In /etc/elog.conf I added:
URL=https://tide1.unh.edu/elog
and restarted elog as above.
Finally, I removed the firewall entry that allowed connections to port 8080 for non-secure elog.
Items of note:
The "apache2-ssl-certificate" created a certificate that seems to expire in 30 days. This obviously not ideal. More details about how to create certificates can be found at HERE. At some point in the future, we'll have to figure this out and create a more appropriate certificate. |