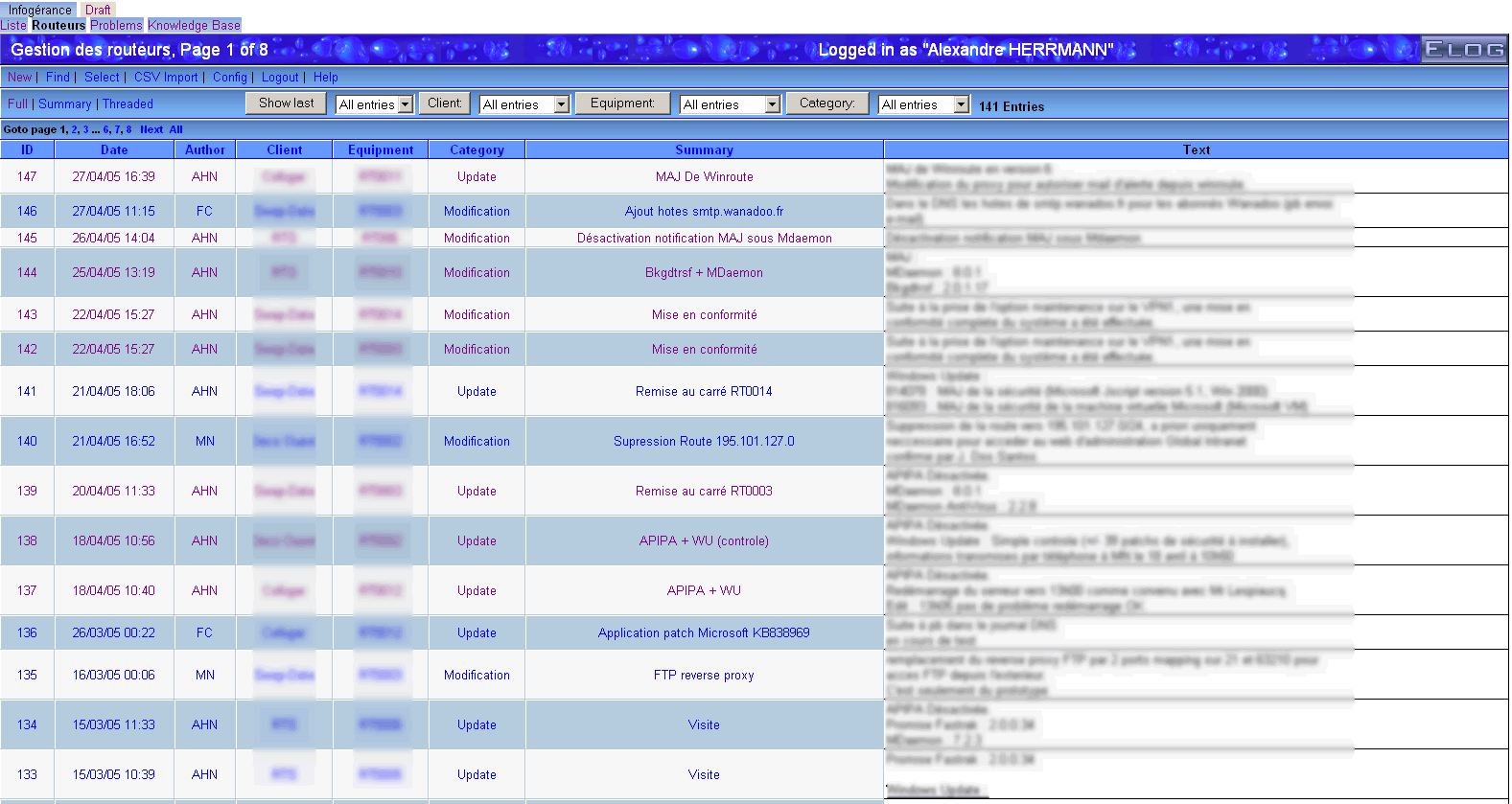
| ID |
Date |
Author |
Author Email |
Category |
Subject |
Status |
Last Revision |
|
19
|
Sat Oct 21 02:23:17 2006 |
Leo Souza | leo@leo.com | Documentation | teste abc | Stable | 1.0 |
| alksjdkajklasjdas |
|
18
|
Mon Sep 25 11:24:05 2006 |
Yoshio Imai | | Documentation | securing of elog with stunnel v4 under Linux | Beta | |
| The following instructions should work in securing the elog using stunnel version 4 under Linux. The specific paths may have to be adapted to your distribution. A sample configuration file is attached. |
| Attachment 1: elog-stunnel4.howto
|
1. Prepare a certificate
------------------------
either: request a certificate for your elog URL from your web administrator
- the private key must not be password-protected
- the 'common name' must be the URL of your elog server
or: create a self-signed certificate yourself with the OpenSSL package
- as root user, create a self-signed certificate with the command
root@localhost:# openssl req -new -x509 -config /etc/ssl/openssl.cnf -keyout stunnel.pem -out stunnel.pem -days 365 -nodes
- this creates a self-signed certificate (-x509) whith one year validity (-days 365)
and no password protection for the private key (-nodes)
- private key and certificate are written to the same file, "stunnel.pem"
Answer all questions, making sure that the 'common name' is the URL under which users
are to reach your elog server.
For more information on how to create and/or manage SSL certificates, see e.g.
http://www.ibiblio.org/pub/Linux/docs/HOWTO/SSL-Certificates-HOWTO
Notice: Unless your web administrator can procure a certificate signed by an established
CA, your elog users will be asked if they want to accept your (unverifiable) certificate
when connecting to your elog server. This is no problem at all but can lead to
questions if your users are unsure about this.
2. Adapt the certificate file to stunnel4 conventions
-----------------------------------------------------
The certificate filename must be the MD5 checksum:
- Retrieve the MD5 checksum of your certificate with
root@localhost:# openssl x509 -hash -noout -in stunnel.pem
abcdefgh
- Rename the certificate file accordingly
root@localhost:# mv stunnel.pem abcdefgh.0
- Move the certificate file to the standard location, e.g. /etc/ssl/certs
- change the permissions of the file to -rw-------
- make sure there is a blank line between
-----END RSA PRIVATE KEY----- and -----BEGIN CERTIFICATE-----
and a blank line after
-----END CERTIFICATE-----
in your certificate file.
3. Configure stunnel4
---------------------
Install the stunnel4 package (if not already done).
Modify the configuration file (e.g. /etc/stunnel/stunnel.conf, depending on your
distribution):
- general options:
cert = /etc/ssl/certs/abcdefgh.0 ; put the name of your certificate file here
debug = 4 ; otherwise ALL connection attempts will be logged to your syslog
pid = /var/run/stunnel4/stunnel.pid ; check where the other services write their pid-files, depends
; somewhat on the distribution
- comment out all lines containing chroot options
- comment out all CA lines
- comment out all service sections except the HTTPS section, which should look as follows
[https]
accept = 443 ; i.e. stunnel listens on port 443, the standard https port
connect = 8080 ; and forwards all connections to port 8080 (use the port under which
; your elogd is running here!)
TIMEOUTclose = 0 ; for buggy MS Internet Explorers, see the stunnel4 manpage
Some Linux distributions require that in the file /etc/defaults/stunnel4 the option ENABLED be set
to ENABLED=1. If not, the stunnel will not be started at system bootup.
4. Start the stunnel4 server
----------------------------
root@localhost# stunnel4 /etc/stunnel/stunnel.conf
Your elog should now be accessible via
https://your.elog.server
|
| Attachment 2: stunnel.conf
|
cert = /etc/ssl/certs/abcdefgh.0
pid = /var/run/stunnel4/stunnel.pid
; Some performance tunings
socket = l:TCP_NODELAY=1
socket = r:TCP_NODELAY=1
; Some debugging stuff useful for troubleshooting
debug = 4
; Service-level configuration
[https]
accept = 443
connect = 8080
TIMEOUTclose = 0
|
|
17
|
Mon Oct 10 18:47:09 2005 |
Exaos Lee | Exaos.Lee@gmail.com | Script | How to run elogd on Gentoo Linux | Stable | Tue Oct 11 08:06:55 2005 by Stefan Ritt |
| I have created some scripts for running elogd on Gentoo Linux. Please untar the attachment and read the file "elogd_gentoo_readme". Any comment is welcomed. |
| Attachment 1: elogd_gentoo.tar.gz
|
|
16
|
Wed Sep 7 16:52:30 2005 |
Peter Eriksson | peter@ifm.liu.se | Other | Solaris 10 SMF/Greenline management manifest for ELog | Stable | |
Please find enclosed as an attachment a Solaris 10 SMF/Greenline manifest that can be used to manage ELog.
(If you don't know what it is - it replaces init.d/cron/inittab and more stuff) |
| Attachment 1: elog.xml
|
<?xml version="1.0"?>
<!DOCTYPE service_bundle SYSTEM "/usr/share/lib/xml/dtd/service_bundle.dtd.1">
<!--
Copyright (c) 2005-06-17 Peter Eriksson (peter@ifm.liu.se)
This manifest can be used to manage an elog daemon using the
Solaris SMF subsystem.
Import this manifest using:
svccfg -v import elog.xml
Then activate the daemon with:
svcadm enable site/elog
-->
<service_bundle type='manifest' name='IFM:elog'>
<service
name='site/elog'
type='service'
version='1'>
<single_instance />
<!-- Need / & /usr filesystems mounted, /var mounted read/write -->
<dependency
name='fs-local'
type='service'
grouping='require_all'
restart_on='none'>
<service_fmri value='svc:/system/filesystem/local' />
</dependency>
<dependency
name='network-service'
grouping='require_all'
restart_on='none'
type='service'>
<service_fmri value='svc:/network/service' />
</dependency>
<dependency
name='name-services'
grouping='require_all'
restart_on='refresh'
type='service'>
<service_fmri value='svc:/milestone/name-services' />
</dependency>
<exec_method
type='method'
name='start'
exec='/ifm/sbin/elogd -D -c /ifm/etc/elogd.cfg'
timeout_seconds='60'>
</exec_method>
<exec_method
type='method'
name='stop'
exec=':kill'
timeout_seconds='30'>
</exec_method>
<instance name='default' enabled='false' />
<stability value='Evolving' />
<template>
<common_name>
<loctext xml:lang='C'>
Electronic Logbook server
</loctext>
</common_name>
<documentation>
<manpage title='elogd' section='1' manpath='/usr/local/man' />
</documentation>
</template>
</service>
</service_bundle>
|
|
15
|
Thu Jul 28 18:42:48 2005 |
Emiliano Gabrielli | AlberT@SuperAlberT.it | Other | [New Feature]: JS calendar filter | Beta | Thu Aug 4 11:20:36 2005 by Emiliano Gabrielli |
NOTE:
it seems that for some strange reason it slows down elog very much when and only when elog is stunneled over ssl!
The attached tarball contains a full featured JavaScript allowing everyone to use a JS calendar (no popup windows, just JS and CSS!) to perform date-based filtering actions. An uncompressed version and the tarball for the last cvs rvision of this script is available at www.SuperAlberT.it
You can browse the ChangeLog here.
A simple way to use it is to uncompress the wall package into the elog data dir, under the "scripts" subdir.
the you can add the following code to your elog.cfg:
Filter Menu text = scripts/calendar_filter/calendar_filter.html
note that this configuration parameter is available in elog starting from
Revision 1.732 2005/07/29
and automagically have the new calendar_filter icon showed 
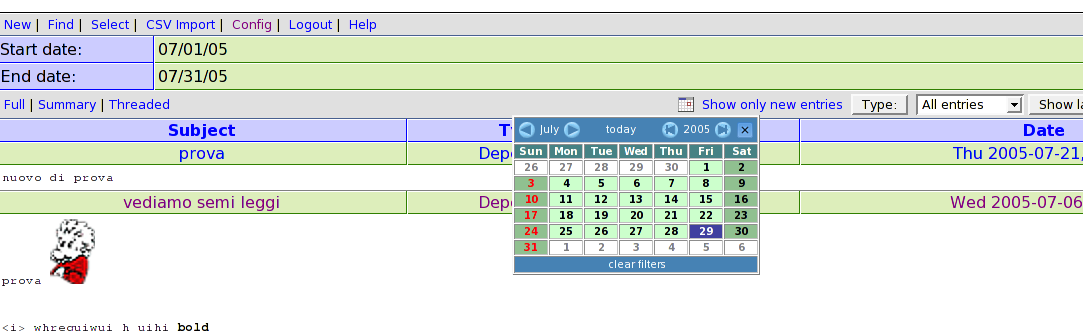 |
| Attachment 2: elog_calendar_filter-1.0.1.tar.gz
|
|
14
|
Fri Jul 8 17:34:02 2005 |
Emiliano Gabrielli | AlberT@SuperAlberT.it | Script | JavaScript list auto-refresh | Stable | Tue Jul 12 12:36:16 2005 by Emiliano Gabrielli |
Here is a simple piece of JS code to accomplish a smart page reload.
We don't reload if in some kind of editing mode.
You can put the code everywhere you like in the elog html page, my suggestion is to put it in Bottom Text (or Top Text):
;auto-refresh
Bottom text = [I]<script language="JavaScript">if (null==window.location.href.match('/[0-9]+$|.*(cmd|select)=.*') ) { window.setTimeout("location.reload();", 2*60*1000); now=new Date(); document.write('<br/>Last reload at '+now.getFullYear()+'/'+(now.getMonth()+1)+'/'+now.getDate()+', '+( ((h=now.getHours())<10) ? '0'+h :h)+':'+( ((m=now.getMinutes())<10) ? '0'+m :m)+':'+( ((s=now.getSeconds())<10) ? '0'+s :s)) }</script>[/I]
the timer is a product of # of minutes, #of seconds and milliseconds... 2 minutes in the above example 
| Revision Tue Jul 12 12:36:16 2005 wrote: |
modified regular expression in order to not activate the auto-refresh in the signle entry view
|
|
|
13
|
Thu Apr 28 15:45:58 2005 |
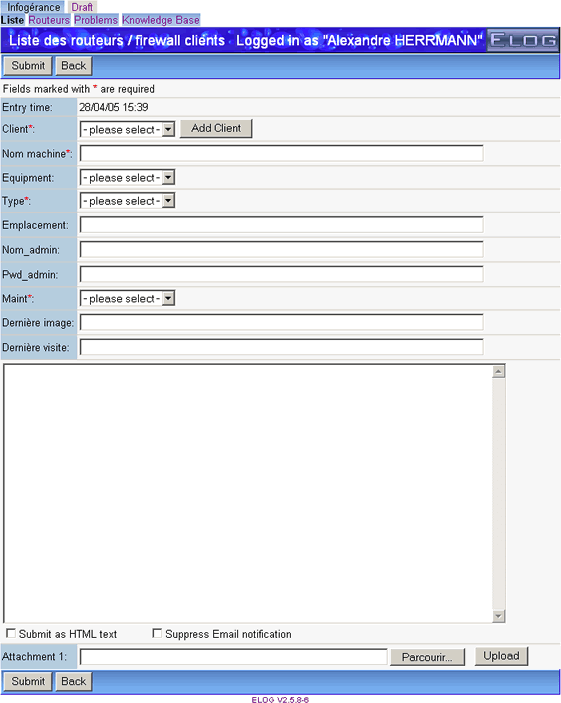
Alex H | alexsynergie-infcom | Theme/Skin | Bubble for pleasure by L'ange noir | Stable | Mon Aug 1 09:35:26 2005 by Alex H |
The original theme is from Francois Cukier but I have change a some color
and font.
Francois Cukier said : "Uncompress "Bubble.zip" in your Elog default
folder if you want to replace the original elog theme. Otherwise, if you
decompress it in another folder, you will need to modify your elogd.cfg
file as described at this adress: http://midas.psi.ch/elog/config.html"
Do it at the same ;o)
I want to thanks Francois Cukier and Stephan Ritt for their works, so
THANKS a lot !
I wait your comments :o).
-UPDATE------------------------------------------------------------------------
2005/08/1 : Alexander Sheremet correct CSS bug thanks to it, archive re-uploaded |
| Attachment 1: bubble2-1.gif
|
|
| Attachment 2: bubble2-2.gif
|
|
| Attachment 3: Bubble.zip
|
|
12
|
Wed Feb 23 11:25:51 2005 |
Emiliano Gabrielli | AlberT@SuperAlberT.it | Script | bash script for thumbnails creation, version: 0.2.0 | Stable | Mon May 2 14:51:29 2005 by Emiliano Gabrielli |
The following script creates a thumbnail for image/ps/pdf files.
it can be used with "Execute edit" and "Execute new" configuration commands
in order to get resized thumbs of attachments.
It uses file(1), convert(1) for images, gs(1) is also required for ps and pdf.
You have to start elogd with the "-x" option to enable execution and put
something similar to the following in you configuration elog file:
Execute new = /path/to/make_thumbs -s 650 -q 95 $attachments
Execute edit = /path/to/make_thumbs -s 100 $attachments
make_thumbs have to be executable by the user running elogd, of course.
ChangeLog:
* version 0.2.0 Fixes a BUG in PDF creation |
| Attachment 1: make_thumbs
|
#!/bin/bash
#
# Makes thumbnails (a jpeg image) from a given set of input files.
# Supported input file types are those supported by 'convert',
# plus PDF.
# Requires convert(1), gs(1) and file(1)
#
# Usage: make_thumbs [options] [ file1 file2 ... ]
# Author: Emiliano Gabrielli
# License: GPL
# Latest Version at http://SuperAlberT.it/download/command_line_scripts/elog/
#
# $Id: make_thumbs,v 1.7 2005/04/14 10:01:37 albert Exp $
function parse_cmdline()
{
export OPTERR=1
while getopts "s:q:Vh" "option" ; do
case "$option" in
s)
MAXSIZE=$OPTARG
;;
q)
QUALITY=$OPTARG
;;
V)
echo "$0 version $VERSION by $AUTHOR"
exit 1
;;
h|*)
echo -e "\nUsage: make_thumb [options] [ file1 file2 ... ]"
echo -e "Options:\n"\
" -s MAXSIZE the size of the thumbnail to be created\n"\
" -q QUALITY the quality of the JPEG image created\n"\
" -V print version and exit\n"\
" -h print this help and exit\n"
exit 1
;;
esac
done
}
function make_thumb()
{
[ ! -z "$1" ] || exit 1
FILE="$1"
# Test if file is readable
if ! [ -r "$FILE" ] ; then
echo "ERROR in $0: $FILE is not readable."
exit 1
fi
THUMBFILE="$FILE.thumb"
EXTENSION="`echo \"$FILE\" | sed 's/.*\.\([^.]*\)$/\1/'`"
# we need this extension in order to instruct 'convert'
# will be renamed at the end of the job
JPEGFILE="$THUMBFILE.jpg"
ROTATE=""
# PDF needs special handling
if [[ `file $FILE | grep "PDF document"` ]] ||
[[ `file $FILE | grep "PostScript document"` ]]
then
# look if we should rotate
DEG=`head -200 $FILE | strings | grep "/Rotate " | head -1 | sed -e 's#.*/Rotate \([0-9]\+\).*#\1#'`
[ ! -z "$DEG" ] && ROTATE="-rotate $DEG"
# Extract first page and convert: PDF -> PS -> JPEG (needs 'gs' and 'convert')
gs -q -dNOPAUSE -dBATCH -r75 -dLastPage=1 -sDEVICE=jpeg -sOutputFile=\|cat "$FILE" | \
convert - $ROTATE -size ${MAXSIZE}x${MAXSIZE} -resize ${MAXSIZE}x${MAXSIZE} -quality $QUALITY +profile "*" "$JPEGFILE" &&
mv "$JPEGFILE" "$THUMBFILE" &
# Else it must be one of the following: postscript, JPEG, GIF, TIFF, RS
elif [[ `file $FILE | grep "\(JPEG\|GIF\|PNG\|TIFF\) image data"` ]] ||
[[ "$EXTENSION" == "rs" ]] || [[ "$EXTENSION" == "RS" ]]
then
convert -size ${MAXSIZE}x${MAXSIZE} "$FILE" -resize ${MAXSIZE}x${MAXSIZE} -quality $QUALITY +profile "*" "$JPEGFILE" &&
mv "$JPEGFILE" "$THUMBFILE" &
fi
}
AUTHOR="Emiliano 'AlberT' Gabrielli"
VERSION="0.2.0"
MAXSIZE=600 # default value
QUALITY=70 # default value
parse_cmdline $@
shift `expr $OPTIND - 1`
for file in "$@" ; do
make_thumb $file
done
# vim:ai:ts=4:sw=4:
|
|
11
|
Wed Nov 24 23:45:19 2004 |
damon nettles | nettles@phgrav.phys.lsu.edu | Other | Steps for securing Elog using SSL and Apache | Stable | |
Everything in this guide was done on a full install of Fedora Core 3 running
Apache 2.0. If you are using an older version of Apache some of this may not
work, so I recommend upgrading. Also, on different Linux distributions, some
of the paths may be different.
The goal here is to get Elog set up under Secure Socket Layers, so that
communication both ways is encrypted. This will cover any password
transactions so nothing gets sent over the web in the clear.
The previous method of securing the Elog, which involved using stunnel, is
out of date. A better way to go is to use the Elog in conjunction with
Apache. The Apache method leverages all the research and development that's
gone into providing secure sockets for Apache, and removes the need for any
serious reinventing of the wheel.
We begin with a web server running on port 80 and an Elog server running on
port 8080.
Making Certificates:
It's necessary to generate some secure certificates to be issued to anyone
who attempts to access the securesite.
A guide to making the certificates can be found at:
http://slacksite.com/apache/certificate.html
So, following the steps in the article:
openssl genrsa -des3 -rand file1:file2:file3:file4:file5 -out\
server.key 1024
where the \ is merely an indicator that the command wouldn't fit on a line
here. The fileN references are sources of random information to help the
random number seed be more random. I merely used some personal text files
that were zipped up, as suggested in the page.
openssl rsa -in server.key -out server.pem
Removes the RSA encryption from the key, to make it easier for the Apache
server to deal with it.
openssl req -new -key server.key -out server.csr
Starts a line of questioning about us as a certificate issuing entity.
Answer with reasonable values.
openssl x509 -req -days 60 -in server.csr -signkey server.key -
out\
server.crt
After this move the server.pem, server.crt, and server.csr to the
appropriate directories under /etc/httpd/conf/ . The extensions explain
which directory to put them in, with the exception that server.pem ended up
in etc/httpd/conf/ssl.key/ .
In the elogd.cfg file, change the port to 8079, and set the URL to
"https://your.host.name/" . Restarting the Elog daemon now leaves us with
Elog listening to port 8079 instead of port 8080.
The rest of the story is in the "elogredirect.conf" file attached to this
post, but here are the highlights.
Create a virtual host dealing with SSL that listens to port 443 (the ssl
port), and acts as a proxy for port 8079 (where Elog is listening). This
allows Apache to act as an SSL handler for Elog by handing off any access at
https://your.host.name/ to the Elog server. The firewall then can keep out
any direct attempts to access port 8079, so that the only thing that can
reach the Elog server is stuff talking to 8079 on the local side of the
firewall (which pretty much means just the Apache proxy). I recommend
Firestarter for the firewall config by the way, it's a real lifesaver.
http://firestarter.sourceforge.net/
This covers the SSL portion of the story, and by doing the redirection
inside the port 443 virtual host, instead of from the port 80 webpage as
before, you can avoid any path overlap.
As was the case for us, you may have links in older Elog posts, e-mails, or
web pages that point to specific Elog posts. If you have been using Elog for
some time and never bothered with the SSL stuff, the links most likely look
something like
http://your.host.name:8080/yourlogbook/postnumber.
To cover legacy support for calls on port 8080, you can create another
virtual host listening to port 8080. This host's job is to take any
incoming URL calls on "http://your.host.name:8080/a_directory" and
translate them into calls on "https://your.host.name/the_same_directory" .
This means that any attempt to contact the Elog on port 8080 will get
answered by an Apache virtual host that redirects the client through the
Apache SSL virtual host described above. See the conf file for the details.
So in the end, the firewall is set to only allow through ports 80, 443, and
8080. Port 80 handles the normal webpage access stuff. Port 443
exclusively handles the SSL port for the Elog daemon, and port 8080
exclusively handles the redirect for the legacy Elog calls.
Implementation of this setup on another system should be pretty
straightforward. Apache's config file is at /etc/httpd/conf/httpd.conf ,
and it also loads any *.conf files in /etc/httpd/conf.d/ . So its a pretty
simple case of just dropping elogredirect.conf into /etc/httpd/conf.d/ and
restarting the Apache server. Of course the necessary changes to elogd.cfg
have to be made and that server restarted as well. The firewall, too, needs
to be setup to secure the whole deal. Note that the elogredirect.conf file
needs to be edited for your specific setup (changing the instances of
"your.host.name" to whatever your server is, and also putting in the
administrator e-mail address where it is noted).
This work was done by Jonathan Hanson and Damon Nettles in the Gravity Lab
at Louisiana State University. You can see our Elog at
https://sam.phys.lsu.edu/elog .
If you have any questions or comments send them to
nettles@phgrav.phys.lsu.edu . |
| Attachment 1: elogredirect.conf
|
### Here be things to make the elogd daemon invisibly secure under an
### Apache SSL proxy virtual host. Arrrrrr!
### ----This config file be mostly written by Jonathan Hanson, 11/23/04
### ----With some help from a few old salts on the net.
### This be the first instance of SSL in our setup, so the SSL module
### Must be called. This can be commented out if it don't put wind in
### your sails.
LoadModule ssl_module modules/mod_ssl.so
### Ahoy, ye scurvy land dogs! Listen to the SSL port (443) or may the
### sea beasts take ye!
Listen 443
### Make a virtual host at the default server name, and assign it port 443.
<VirtualHost _default_:443>
### Here be standard configuration for the Virtual Host
ServerAdmin your_e-mail_address
ServerName _default_:443
RequestHeader set Front-End-Https "On"
### This be the path to the elog directory
### (This didn't seem to make any difference, but it be a good
### idea nonetheless)
DocumentRoot /usr/local/elog
### Here be the setup for the SSL component of the Virtual Host
SSLEngine On
SSLCertificateFile /etc/httpd/conf/ssl.crt/server.crt
SSLCertificateKeyFile /etc/httpd/conf/ssl.key/server.pem
### Here be the setup options for the Proxy module
ProxyRequests Off
ProxyPreserveHost On
### This be the root of the new Virtual Host, and it should be
### redirected to the port the elogd server is listening to
### (8079 on our poop deck).
<Location />
ProxyPass http://your.host.name:8079/
ProxyPassReverse http://your.host.name:8079/
SSLRequireSSL
</Location>
### Shiver me timbers! A firewall can be laid across the elog
### port to hinder direct access from the outside world to the elog
### daemon. This'll make the scurvy wretches come in through the apache
### proxy virtual host, and batten down the hatches on the elog in general.
</VirtualHost>
### Our previous elog configuration was at http://your.host.name:8080 and some of our
### users made static HTML links to other posts in their posts and email. They be sleeping
### in Davy Jones's locker in the briney deep now, but we be needing to make these posts
### backward-compatible. We be changing the port Elogd listens to (as above) to 8079, and
### then we be using another new virtual host at port 8080 to redirect to the new SSL URL.
### So it appears to the landlubbers outside as if a normal elog server is listening to port
### 8080, but in reality it be a Virtual Host redirecting through the other SSL virtual host
### which then be passing it on to the port the elog server really be listening to.
### If ye not be needing this backwards compatability, the following section can be made
### to walk the plank.
### I won't be telling ye twice, ye slimy bilge rat! Pay attention to what
### used to be the old elog port(8080).
Listen 8080
<VirtualHost _default_:8080>
### Here be standard configuration for the Virtual Host
ServerAdmin your_e-mail_address
ServerName _default_:8080
### This be the path to the html directory
### (This didn't seem to make any difference, but it be a good
### idea nonetheless)
DocumentRoot /httpd/html
### Here be the dark magic of mod_rewrite. Quake in your boots ye dogs!
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteRule ^/(.*) https://your.host.name/$1 [NC,R=301,L]
</IfModule>
</VirtualHost>
### In the end, elog be reachable through either https://your.host.name/
### or http://your.host.name:8080/ , though the latter will be rewritten
### to the former as soon as the request be made. This be satisfying our
### needs for backwards compatbility with old URLs, while ensuring modern
### secure SSL support. Beware matey, recognize that we also had to change
### the port that elog listens to, and then add a URL line in the elogd.cfg
### file:
### port = 8079
### URL = https://your.host.name/
### Also a firewall was brought up and told to allow through only ports
### 80(html), 443(SSL), and 8080(the elog stand-in) and of course any other
### ports ye may need for other applications.
|
|
10
|
Fri Sep 24 23:14:47 2004 |
Sridhar Anandakrishnan | sak@essc.psu.edu | Script | Perl script to forwar emails to elog | Alpha | |
Takes one or more files from the command line that contain MIME
messages, and explodes their contents out into /tmp. The parts
are sent to elog as attachments. |
| Attachment 1: doelog
|
#!/usr/bin/perl -w
=head1 NAME
doelog - save a mime message to elog
=head1 SYNOPSIS
doelog <mime-msg-file> <mime-msg-file> ...
someprocess | doelog -
=head1 DESCRIPTION
Takes one or more files from the command line that contain MIME
messages, and explodes their contents out into /tmp. The parts
are sent to elog as attachments.
Modified mimeexplode of the MIME::Tools in perl
This was written as an example of the MIME:: modules in the
MIME-parser package I wrote. It may prove useful as a quick-and-dirty
way of splitting a MIME message if you need to decode something, and
you don't have a MIME mail reader on hand.
=head1 COMMAND LINE OPTIONS
None yet.
=head1 AUTHOR
sak@essc.psu.edu
=cut
BEGIN { unshift @INC, ".." } # to test MIME:: stuff before installing it!
require 5.001;
use strict;
use vars qw($Msgno $cmd);
use MIME::Parser;
use Getopt::Std;
## these should be options too?
## base elog cmd
$cmd = "~/elog -h localhost -p 8080 ";
#------------------------------------------------------------
# dump_entity - dump an entity's file info
#------------------------------------------------------------
sub dump_entity {
my $ent = shift;
my @parts = $ent->parts;
my $file;
die "too many attachments\n" if ($#parts>10);
if (@parts) { # multipart...
map { dump_entity($_) } @parts;
}
else { # single part...append to elog cmd
$file = $ent->bodyhandle->path;
$cmd .= "-f \"$file\" ";
## print $cmd, "\n";
## print " Part: ", $ent->bodyhandle->path,
## " (", scalar($ent->head->mime_type), ")\n";
}
}
#------------------------------------------------------------
# main
#------------------------------------------------------------
sub main {
my $file;
my $entity;
my $subject;
my $logbook;
our($opt_l);
# Sanity:
## (-w ".") or die "cwd not writable, you naughty boy...";
## check if user wants a particular logbook
## fix to add host and port?
getopts('l:');
if($opt_l) { $logbook=$opt_l;} else {$logbook="emails";}
$cmd .= "-l $logbook ";
# Go through messages:
@ARGV or unshift @ARGV, "-";
while (defined($file = shift @ARGV)) {
# Create a new parser object:
my $parser = new MIME::Parser;
# Optional: set up parameters that will affect how it extracts
# documents from the input stream:
$parser->output_under("/tmp");
# Parse an input stream:
open FILE, $file or die "couldn't open $file";
$entity = $parser->read(\*FILE) or
print STDERR "Couldn't parse MIME in $file; continuing...\n";
close FILE;
## get the subject, assumes all logbooks have a subject
## attribute - not necessarily true. Mine do...
chomp($subject = $entity->head->get('Subject', 0));
$cmd .= "-a subject=\"$subject\" ";
print $cmd, "\n";
# Congratulations: you now have a (possibly multipart) MIME entity!
dump_entity($entity) if $entity;
### $entity->dump_skeleton if $entity;
### print $cmd, "\n";
exec $cmd;
}
1;
}
exit (&main ? 0 : -1);
#------------------------------------------------------------
1;
|